Managing a Security Operations Center (SOC) can be a complex and challenging task. SOC Managers are responsible for ensuring the security of their organization's networks, systems, and data. However, they often face several challenges that can hinder their effectiveness.
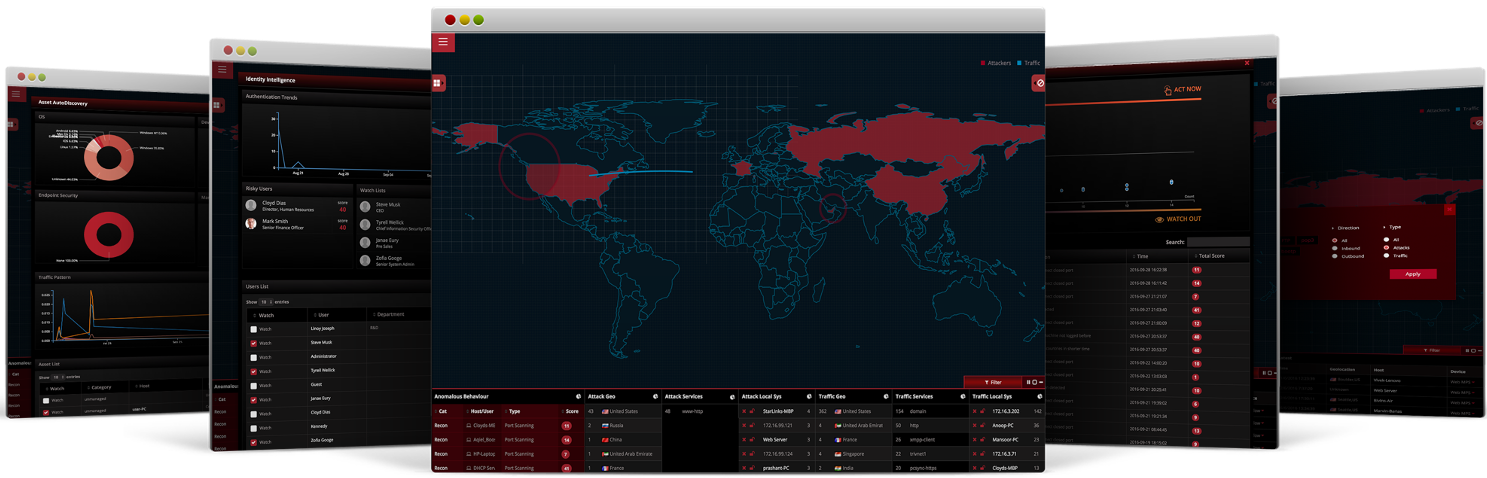
The LinkShadow Cyber Mesh Security Architecture offers a more integrated, dynamic, and proactive approach to cybersecurity compared to the traditional siloed approach. By consolidating security into a cyber mesh platform, organizations can enhance their visibility, agility, and overall security posture.